More than the act of testing, the act of designing tests is one of the best bug preventers known.
Penetration testing – whether it’s internal or external, white-box or black-box – uncovers critical issues and demonstrates how well your network and information assets are protected. Because Macksofy Technologies thinks and acts like an attacker, you can discover critical vulnerabilities and remediate them before they are exploited.
Pen Testers actively attempt to ‘exploit’ vulnerabilities and exposures in a company’s infrastructure, applications, people and processes. Through exploitation, Macksofy Technologies is able to provide context around the vulnerability, impact, threat and the likelihood of a breach in an information asset. It is frequently possible for a pen tester to gain remote access to operating systems, application logic and database records. Through active exploitation of direct and interconnected systems, Nettitude can provide strategic guidance on risk and tailored advice on counter measures.
Type Of Penetration Testing
Internal Penetration Testing
This type of testing assesses security through the eye of an internal user, a temporary worker, or an individual that has physical access to the organisations’ buildings over its Local Area Network (LAN) or through Wi-Fi networks.The tests will observe whether it is possible to gain access to privileged company information from systems that are inside the corporate firewalls.
External Penetration Testing
This type of testing assesses an organizations infrastructure from outside of the perimeter firewall on the Internet. It assesses the environment from the vantage point of an internet hacker, a competitor or a supplier with limited information about the internet facing environment.
What We Test?
Testing is an infinite process of comparing the invisible to the ambiguous in order to avoid the unthinkable happening to the anonymous.

WEB APPLICATION PENETRATION TEST
Modern web applications handle increasingly sensitive data, so it is important to ensure that they are very secured
Know More
NETWORK PENETRATION TEST
Focused network infrastructure penetration testing aiming to identify network and system level flaws
Know More
Mobile Penetration Testing
With such a surge in mobile application development, attack surfaces have increased remarkably.
Know More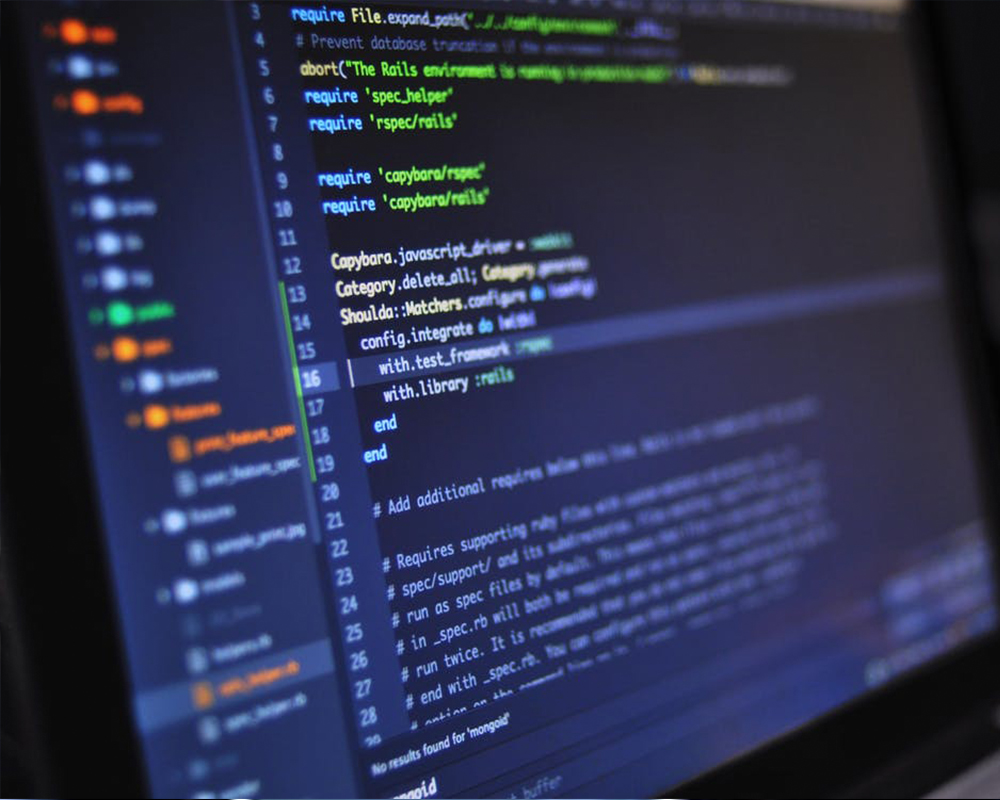
Cloud Penetration Testing
Shared services have become extremely common so security plays an important role.
Know More
Firewall Penetration Testing
Able to assess the rulebase, the published services and the in-built security daemons of any firewall.
Know More
Code Penetration Testing
Code review is probably the single-most effective technique for identifying security flaws.
View ProjectMacksofy Technologies Penetration Testing Methodology
How Does it Works